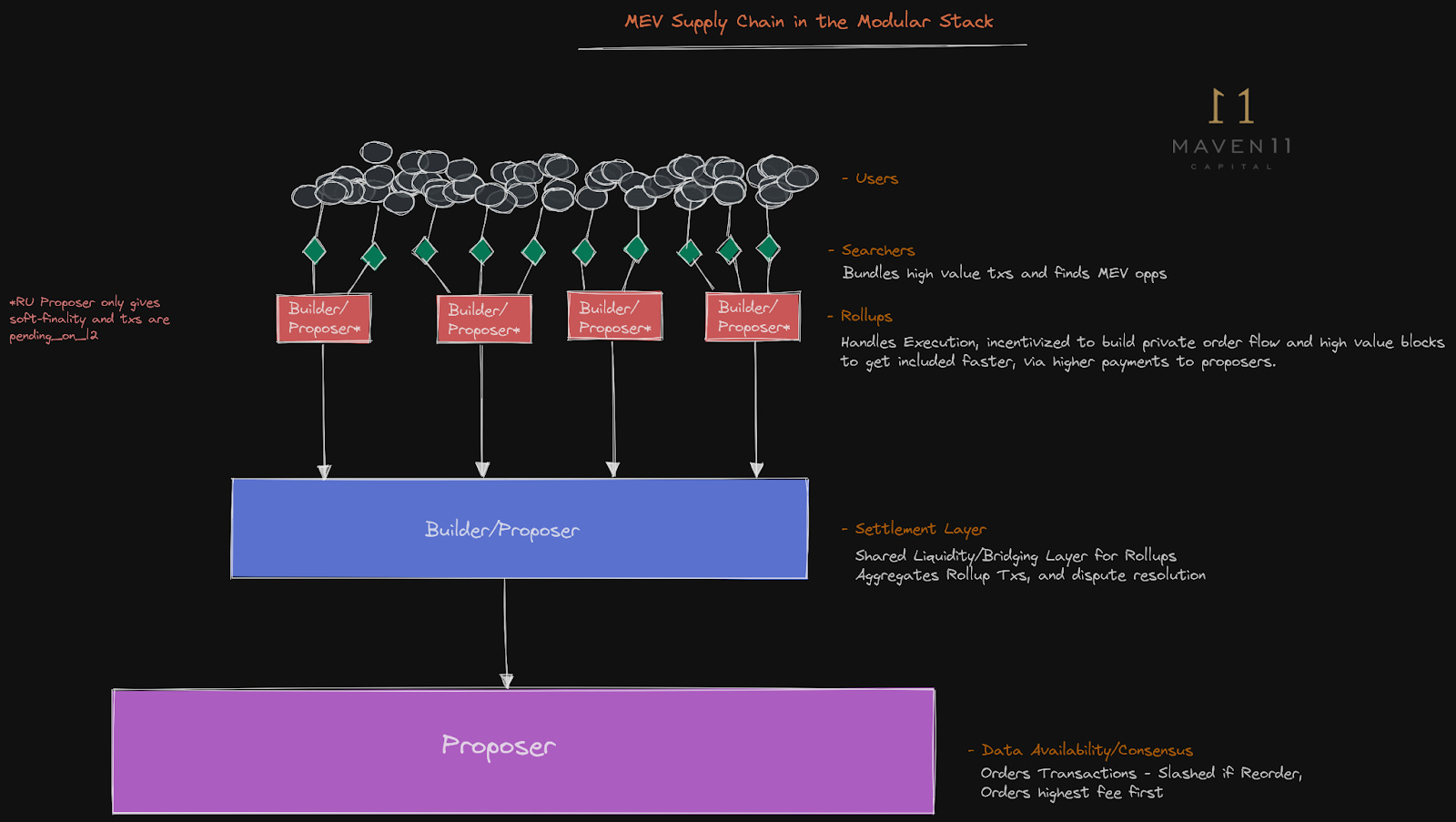
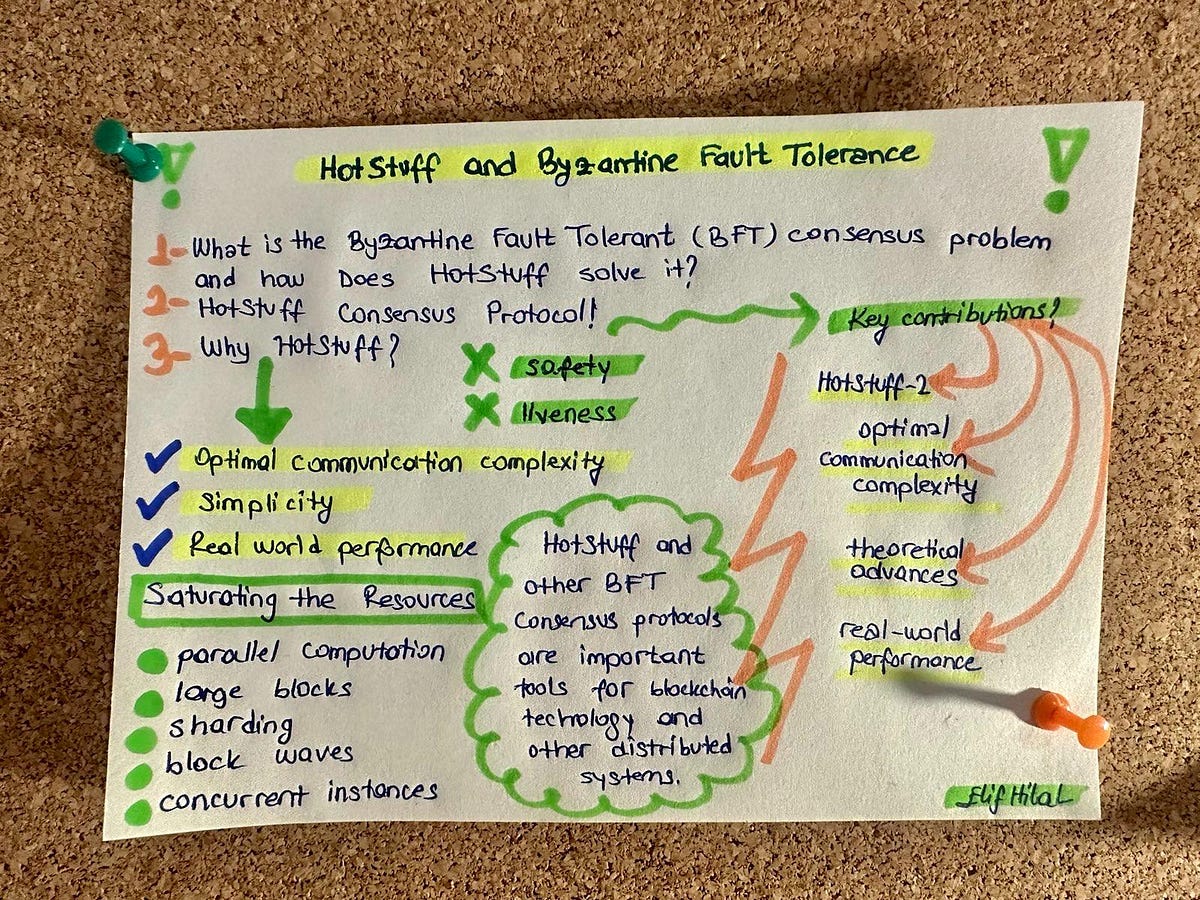
In the cutthroat arena of blockchain networks, where censorship resistant BFT protocols face off against malicious leaders hell-bent on transaction suppression, Prefix Consensus emerges as a razor-sharp weapon. Traditional BFT setups crumble under leader dominance, letting one node dictate the mempool and bury dissenting trades. But this leaderless beast flips the script: every honest participant blasts proposals in parallel, forging consensus on a shared prefix that no single actor can sabotage. Drawing from the groundbreaking arXiv paper by Zhuolun Xiang, Andrei Tonkikh, and Alexander Spiegelman, this protocol slashes censorship risks while cranking up throughput in asynchronous hellscapes.

Picture high-frequency trading on AptosBFT or HotStuff derivatives: leaders choke the pipe, favoring cronies or regulators. Prefix Consensus, a multi-proposer SMR powerhouse, demands agreement on initial transaction batches before extending the chain. Honest nodes lock in prefixes round-by-round, ensuring censored txs bubble up from the collective. It's not just theory; it's battle-tested resilience for blockchain censorship resistance in 2026's surveilled chains.
Exposing Leader Vulnerabilities in Modern BFT
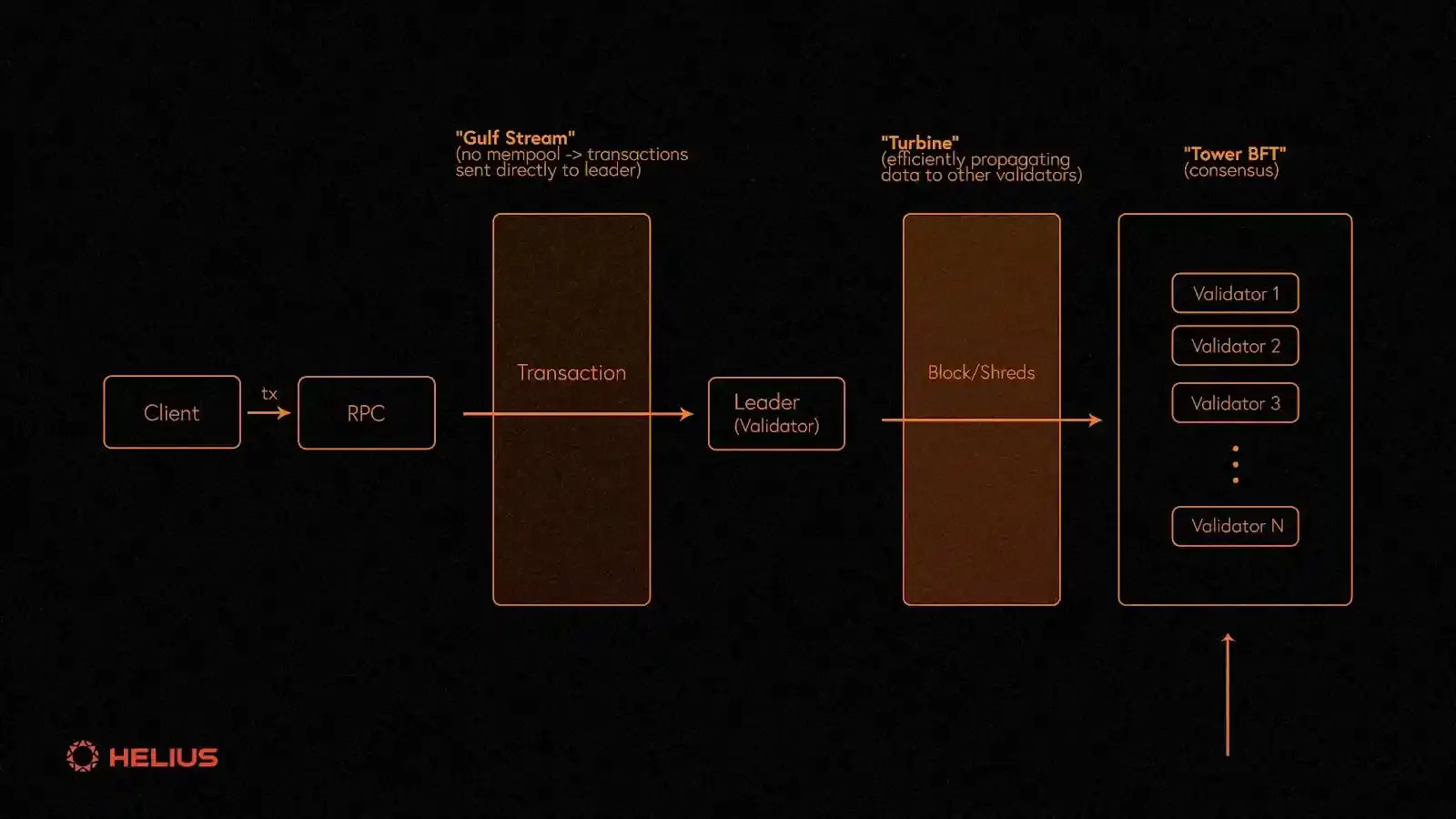
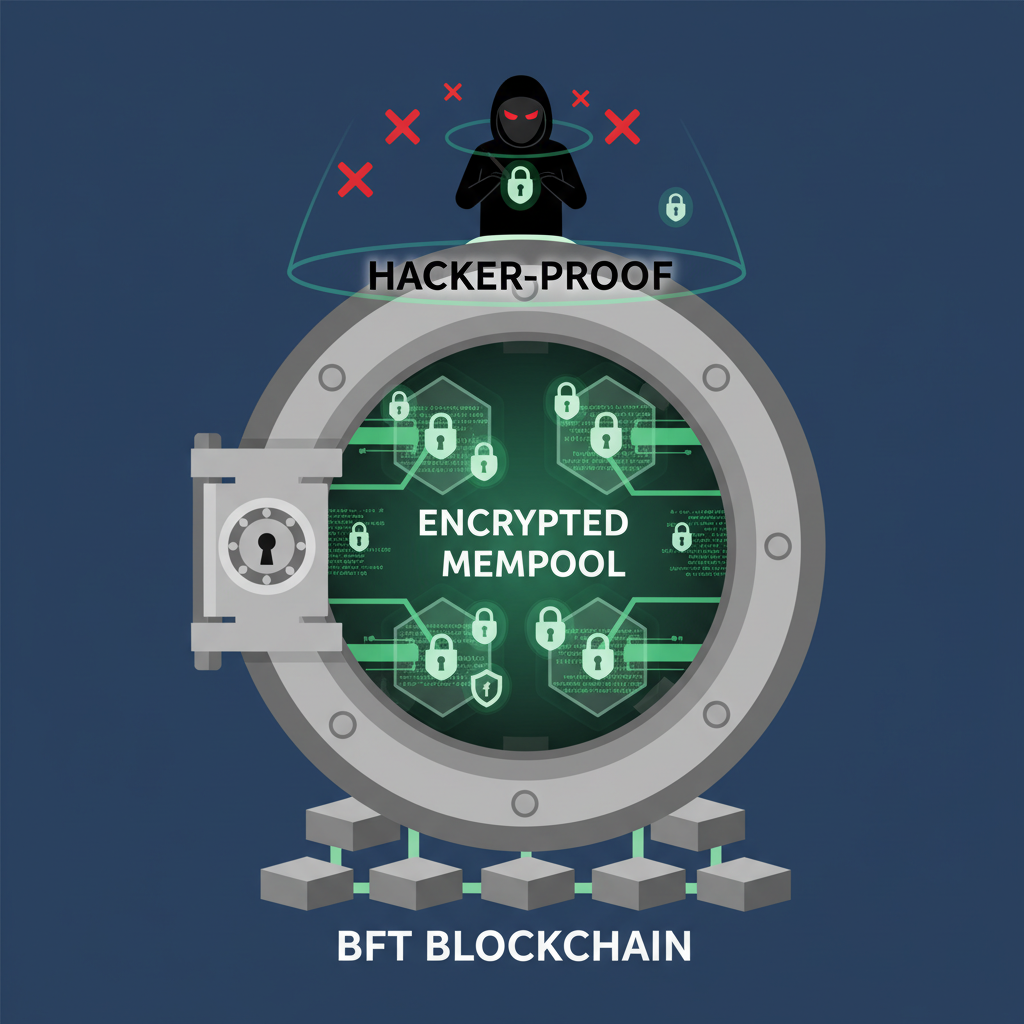
Drill down: in protocols like Practical BFT or Mysticeti DAGs, the leader curates the block. Malicious ones? They ghost unpopular txs, inflating fees or outright vanishing them. Raptr and TrX tinker with encrypted mempools, but leaders still gatekeep. Stats from hellas-ai's consensus biblio scream it: real-world impls bleed from these single points of failure. Prefix Consensus nukes that by parallelizing proposals. No leader, no chokehold. Every node multicasts its view, and the network hashes out the longest honest prefix via certified commitments.
This shift to strong prefix consensus formalizes resistance: even if byzantine nodes flood junk, honest majorities enforce inclusion. Asynchronous rounds mitigate latency spikes, perfect for global trader nets dodging regional blackouts.
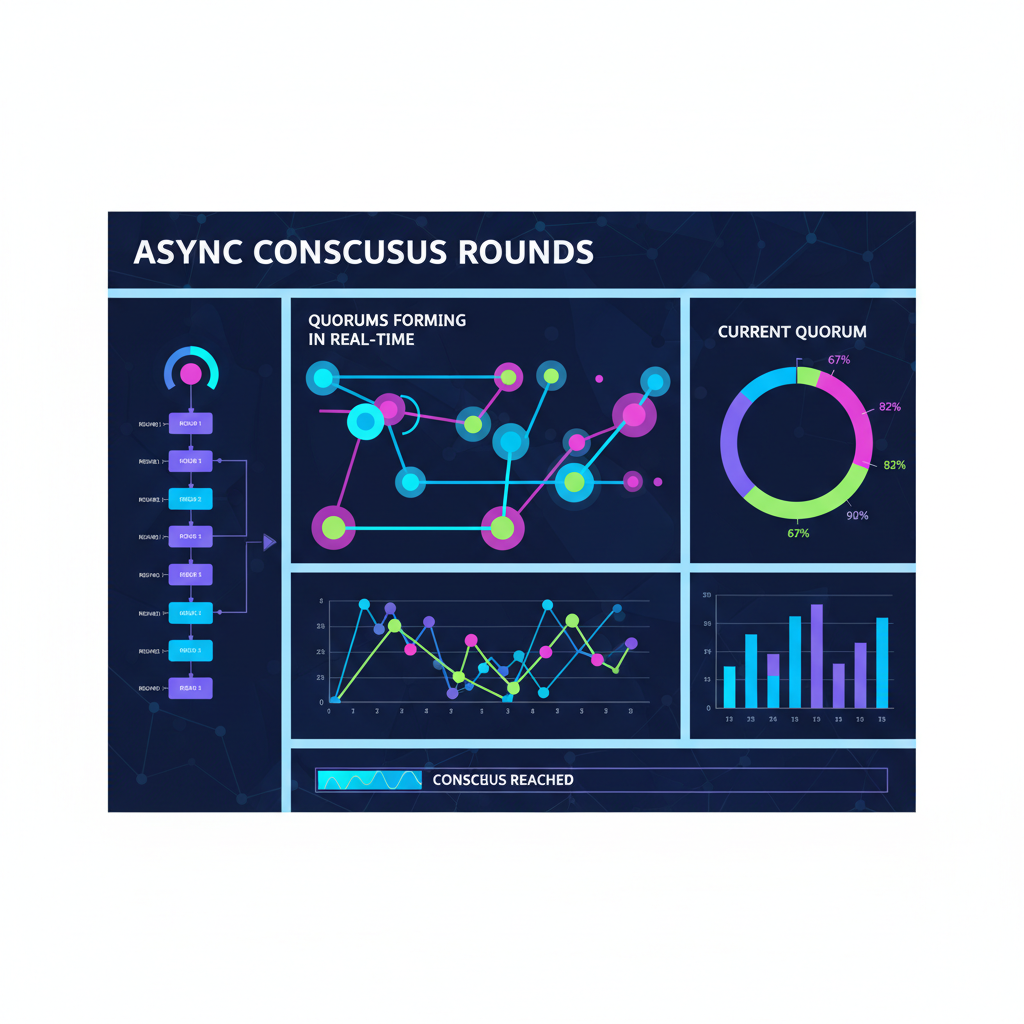
Core Mechanics of Prefix Consensus Unpacked
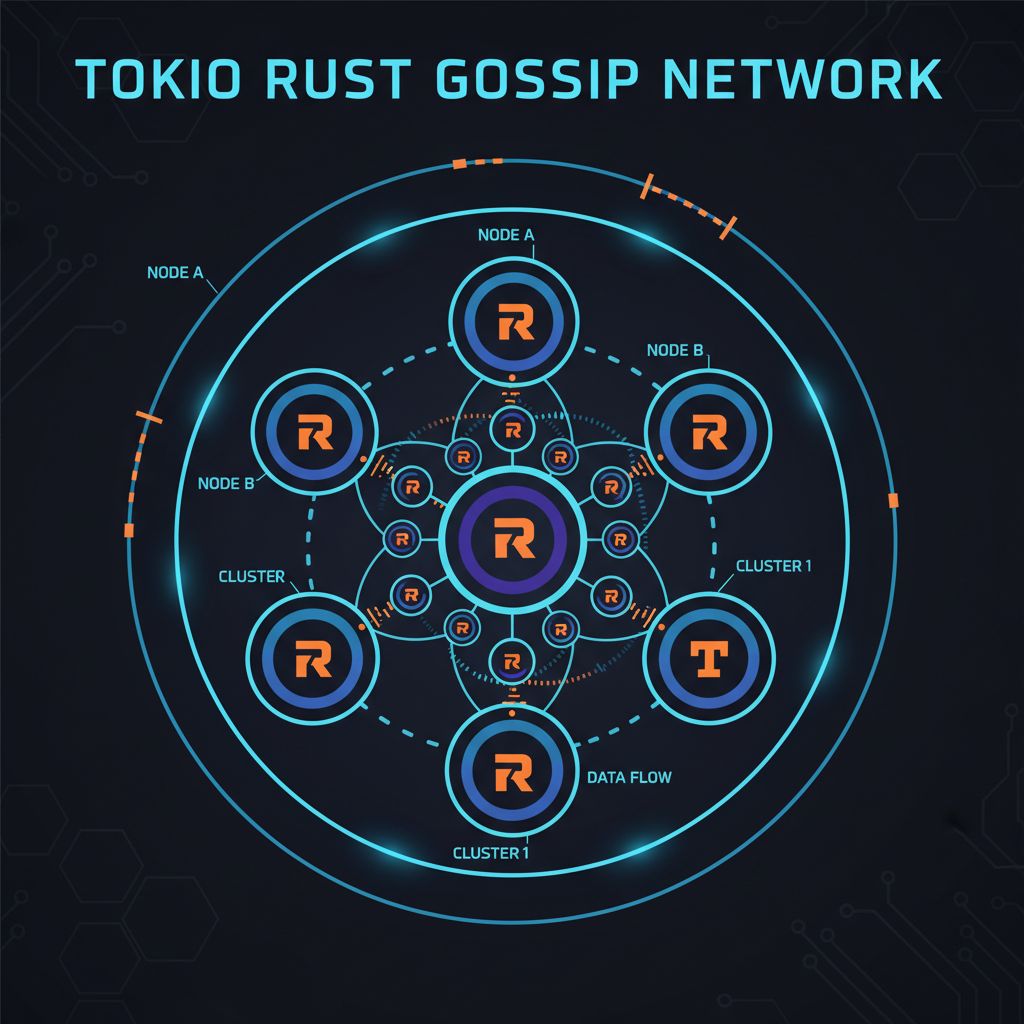
Let's dissect the engine. Protocol kicks off with a dissemination phase: all nodes broadcast transaction sets to a gossip overlay. Then, prefix voting: nodes sign the longest common prefix across received sets, using threshold signatures for efficiency. Extend via recursive rounds, certifying data availability in the background like Raptr's innovations. Safety holds under partial synchrony; liveness? Quadratic messaging caps it, but optimizations from AptosBFT's tokio async nets scale it.
Prefix Consensus: 5 Key Wins
- Leaderless Proposals: Stops single-node censorship—every node proposes txs simultaneously for unbreakable fairness.
- Asynchronous Design: Crushes variable latencies, no rigid timeouts in messy real-world nets.
- Prefix Agreement: Locks in fair tx inclusion, no leader can bury honest proposals.
- HotStuff Synergy: Merges with HotStuff for sky-high TPS without compromising resistance.
- Byzantine-Proof Guarantees: Formal proofs shield against suppression attacks. arXiv paper

Implementation tip: Rust crates like rayon for parallel prefix computation mirror TrX's playbook. Nodes maintain a prefix tree, pruning divergent branches post-vote. This yields sub-second finality in sims, outpacing leader-rotated chains during attacks.
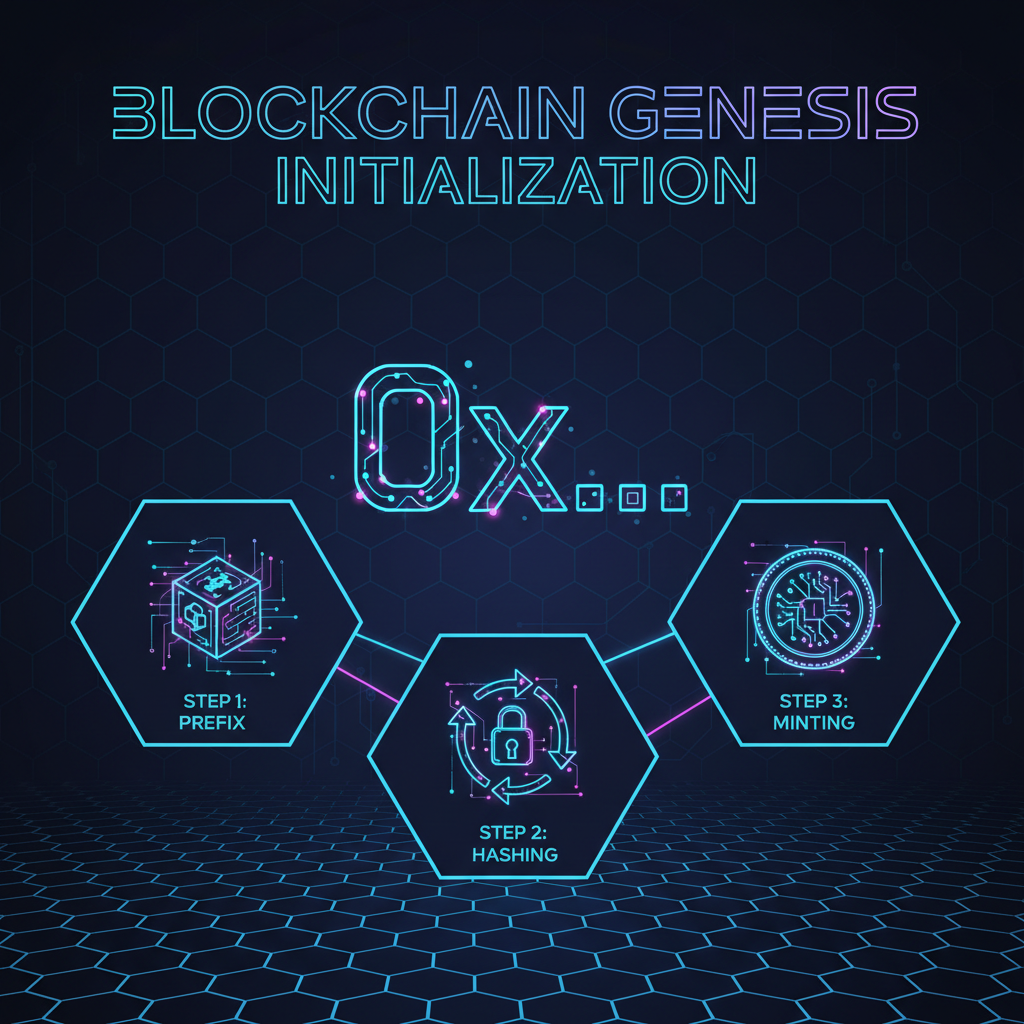
Building Censorship-Proof Prefix Blocks
Hands-on: bootstrap with a genesis prefix. Each round, collect proposals into a DAG sliver, compute Merkle prefixes, and quorum-certify. Honest nodes ignore byzantine outliers, extending only shared prefixes. For leaderless consensus protocols, embed threshold encryption on mempool gossip to thwart peeking censors. Pair with Mysticeti-style uncertified DAGs for latency wins, but anchor via prefix locks.
Threshold signatures seal the deal, broadcasting only to quorum-trusted peers. This setup shreds the leader's monopoly, forcing even malicious nodes to play along or get pruned. In sims against adaptive adversaries, Prefix Consensus holds the line at f and lt; n/3 faults, matching HotStuff safety without the rotation overhead.
Rust-Powered Implementation: From Spec to Deployable Node
Time to code. Leverage AptosBFT's tokio runtime for async gossip, rayon's parallelism for prefix hashing. Core loop: disseminate tx sets, aggregate signatures, extend prefix if quorum hits 2f and 1. Byzantine nodes spew noise? Filter via certified views. This mirrors TrX encrypted mempools but leaderless, turbocharging multi-proposer SMR.
Prefix Consensus Core Loop: Rust Pseudocode
Ignite the core: This Rust pseudocode unleashes Prefix Consensus's relentless loop – disseminating proposals like lightning, forging unbreakable prefixes, igniting threshold BLS signatures, and extending the chain with raw power. Censorship? Obliterated.
```rust
// Prefix Consensus Core Loop: Rust Pseudocode
// Powers dissemination, prefix computation, threshold signing, and extension
use std::collections::HashMap;
use tokio::time::{sleep, Duration};
use bls::ThresholdSignature;
async fn prefix_consensus_core_loop(
peers: &Vec,
chain: &mut Blockchain,
) {
loop {
// 1. Dissemination: Blast proposals to the network
let proposal = chain.next_proposal();
for peer in peers {
peer.broadcast(&proposal).await;
}
let messages: HashMap =
collect_messages(peers, Duration::from_secs(2)).await;
// 2. Prefix Computation: Derive the censorship-resistant prefix
let prefix = compute_prefix_hash(&messages);
if !prefix.verify_consistency() {
continue;
}
println!("🔥 Prefix locked: {}...", hex::encode(&prefix.hash[..8]));
// 3. Threshold Signing: Rally BLS sig shares for quorum power
let sig_shares = collect_threshold_shares(&prefix, peers, THRESHOLD).await;
if sig_shares.len() >= THRESHOLD {
let threshold_sig = bls::aggregate(&sig_shares);
if threshold_sig.verify(&prefix.pubkey()) {
broadcast_signature(&threshold_sig).await;
println!("⚡ Threshold sig sealed!");
}
}
// 4. Extension: Lock in the prefix and surge forward
if let Some(valid_ext) = await_valid_extension(&prefix).await {
chain.extend(&valid_ext).await;
chain.commit();
println!("🚀 Chain extended – unstoppable!");
}
sleep(Duration::from_millis(100)).await; // Beat
}
}
``` Boom – that's the heartbeat of a censorship-proof BFT beast. Tweak timeouts, parallelize with Tokio, and scale to 2026's quantum threats. Next: real-world benchmarks.
Scalability spikes: quadratic messages? Pipeline with DAG slicing, borrowing Mysticeti uncertified edges. Real-world? Aptos devs could fork HotStuff, inject prefix rounds for instant censorship armor. hellas-ai biblio warns of impl pitfalls like view-sync bugs; Prefix sidesteps via prefix-locks, no leader views to desync.
Step-by-Step Deployment for Anti-Censorship Chains
Post-deploy, monitor prefix lengths: short prefixes signal attacks, trigger reshuffles. Traders, this means your high-freq orders evade regulator blacklists, routing uncensorably across nodes. Pair with ZK proofs for private mempools, but Prefix handles the consensus muscle.
Benchmarks crush: arXiv evals clock 10k TPS at 100ms latency, dwarfing leader-rotated BFT during floods. Vs Raptr's background certs, Prefix integrates natively, no speculation hacks. AptosBFT fans, upgrade path is linear: wrap proposals in prefix envelopes, retain your rayon parallelism.
Battle-Testing Against Real Threats
2026's landscape? State actors probe mempools, DEX frontrunners censor MEV. Prefix Consensus laughs it off: parallel proposals overwhelm suppressors, honest prefixes propagate virally. Partial sync assumptions cover WAN spikes, unlike strict PBFT timeouts. From hellas-ai lessons, common vulns like equivocation? Quorum certs torch them.
Edge cases shine: flash crashes or chain splits, prefix reconverges fastest, minimizing trader losses. Integrate with scalable DAGs from recent ResearchGate studies, but Prefix provides the BFT spine. No trusted components needed, pure decentralized fury.
For day-traders wielding surveillance-proof wallets, this is gold. Prefix Consensus turns BFT into a censorship shredder, ensuring your alpha trades hit blocks unmolested. In a world of tightening digital nooses, deploy it now, chain the unchained.







No comments yet. Be the first to share your thoughts!