In the evolving landscape of Layer 2 scaling solutions, centralized sequencers pose a subtle yet profound threat to the ethos of decentralization. These single points of control not only risk downtime from failures but, more critically, enable subtle censorship by withholding or reordering transactions at whim. Threshold signatures emerge as a robust antidote, distributing signing authority across a quorum of nodes to enforce fair transaction ordering in blockchain environments. By requiring consensus from a threshold subset, they fortify L2 censorship resistance without sacrificing the speed that makes rollups viable.
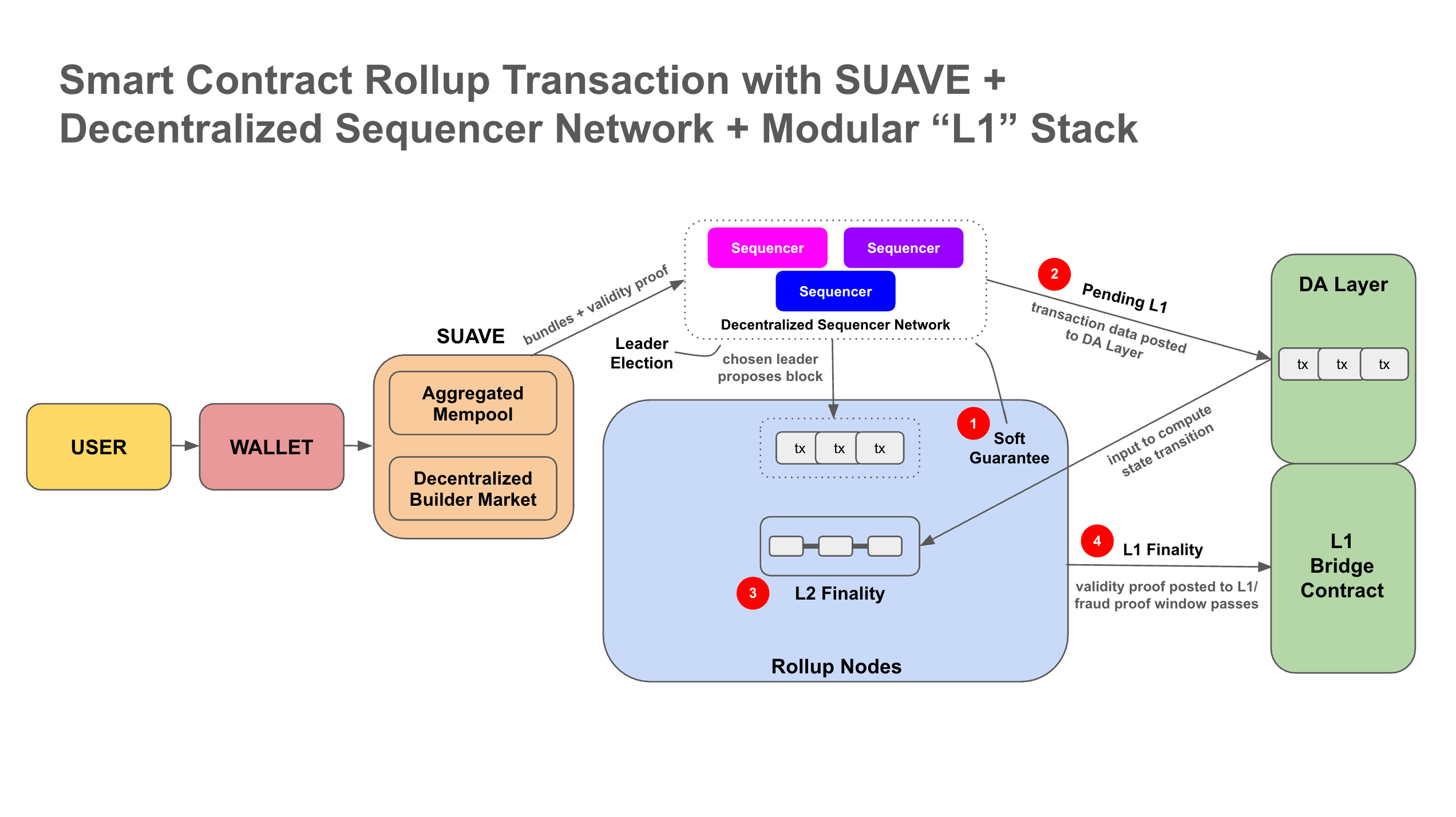
Recent innovations, like Metis's decentralized sequencer pool leveraging threshold signature schemes, underscore this shift. Projects such as Morph and shared sequencer networks from Maven 11 highlight how TSS-based multi-party computation can deliver liveness and sovereignty. Yet, implementation demands caution; poor design invites collusion risks or inefficient communication, as noted in arXiv analyses of proposal latencies.
Navigating Sequencer Centralization Risks
Traditional L2 sequencers, often a solitary node or small cluster, batch transactions into compressed proofs for Layer 1 settlement. This efficiency comes at a cost: a private mempool invites selective inclusion, echoing the censorship resistant L2 sequencer dilemma outlined in Arbitrum docs and Quantstamp's security frameworks. Escape hatches mitigate some issues, but they rely on timely detection and Layer 1 enforcement, which can lag in adversarial scenarios.
Decentralized alternatives redistribute this power. A pool of sequencers collectively orders transactions, but without cryptographic glue, malicious actors could dominate. Threshold signatures bridge this gap, ensuring only threshold-approved blocks proceed. FROST protocols, for instance, optimize for Schnorr signatures with two-round efficiency, slashing communication overheads to linear scales in happy paths.
Real-World TSS Deployment Challenges and Wins in L2 Sequencer Networks
| Challenge | Solution | Impact |
|---|---|---|
| Complexity of Distributed Key Generation (DKG) in sequencer pools | Feldman Verifiable Secret Sharing (VSS) for secure share distribution (e.g., Metis decentralized sequencer pool) | Establishes shared public key with distributed secret shares, preventing single-point key compromise |
| High latency in traditional multi-round TSS signing | FROST protocol for efficient two-round Schnorr/EdDSA threshold signatures | Achieves linear communication and reduces proposal latency to ~7δ in happy path (arXiv) |
| Censorship risks from centralized sequencers | TSS-based shared sequencer networks (e.g., Morph, Maven 11 shared sequencer) | Distributes signing authority for liveness and censorship resistance without compromising rollup sovereignty |
| Sequencer node failures and key management | HSMs/TEEs for shares + dynamic resharing protocols (luxfi/threshold library) | Enables resilience to failures/additions without downtime or key reconstruction |
| Scalability for large-scale decentralized networks | Practical zero-trust TSS libraries supporting 20+ blockchains | Enhances security in cryptocurrency systems via distributed signing (Cryptology ePrint) |
| Vulnerability to future quantum attacks | Lattice-based post-quantum threshold signature schemes | Future-proofs L2 sequencers against quantum computing threats (Chainscorelabs) |
Core Principles of Threshold Signature Schemes
At heart, threshold signatures splinter the private key into shares via secret sharing polynomials, verifiable through commitments like Feldman's VSS. No single node reconstructs the full key, thwarting compromise. During signing, participants engage in an interactive protocol: each computes partial signatures on the block hash, aggregates them, and verifies against the public key.
This setup demands careful parameter selection - a t-of-n threshold where t exceeds n/2 for security, yet low enough for liveness. In decentralized sequencer implementation, integrate with proposer-builder separation; sequencers propose, threshold signs, then posts to Layer 1. Resilience mechanisms, like dynamic resharing, handle churn without key migration pains.
Post-quantum threats loom, urging lattice-based schemes over ECDSA derivatives. Libraries like LuxFi's threshold repo support 20 and chains, easing adoption while embedding quantum resistance.
The foundation of any threshold signatures sequencer lies in Distributed Key Generation (DKG), a ceremony where nodes collaboratively forge the group key sans trusted dealer. Each acts as dealer sequentially or in parallel: generate a secret polynomial, encrypt shares for peers, broadcast commitments.
Implement Feldman VSS for verifiability; nodes challenge shares to detect malice, disqualifying cheaters via complaints. Output: a joint public key for block signing, plus Lagrange coefficients for later aggregation. Chainscore guides emphasize HSM or TEE storage for shares, critical against side-channels.
Consider a 10-node pool with t=7: DKG yields shares s_i, verifiable poly f(x) = s and a1 x and. . . and a_{t-1} x^{t-1}. Post-DKG, refresh periodically to counter leakage, using proactive secret sharing.
Once DKG completes successfully, the network possesses a shared public key ready for block production. Periodic refreshes via proactive secret sharing mitigate gradual key wear from potential leaks, ensuring long-term viability without full ceremonies.
Executing Threshold Signing in Sequencer Pools
With keys in place, the signing phase activates during block proposal. A lead sequencer gathers transactions from a shared mempool, orders them fairly - perhaps via time-stamps or VRFs for fair transaction ordering blockchain - and broadcasts the candidate block hash. Threshold nodes then run the two-round FROST protocol: Round 1 generates nonces and partial sigs; Round 2 aggregates into a single signature indistinguishable from a lone signer.
FROST Threshold Signing Rounds Pseudocode (Rust-style)
Implementing FROST for threshold signing of L2 block hashes in sequencer nodes enhances censorship resistance but introduces complexities in coordination and verification. Mishandling rounds can lead to invalid signatures or security flaws. The following pseudocode illustrates the two-round process cautiously, assuming a BLS12-381 curve; real-world use demands rigorous testing against known attacks like rogue-key.
```rust
// Simplified Rust pseudocode for FROST signing rounds in an L2 sequencer node.
// WARNING: This is for illustrative purposes only. Production implementations
// require full verification, secure networking, and cryptographic audits.
use rand::Rng;
type Scalar = blst::SecretKey; // Simplified
type G1Point = blst::PublicKey;
type G2Point = blst::P1Affine; // Placeholder types
type Commitment = (G1Point, G2Point);
type SigningShare = Scalar;
// Round 1: Each participant generates a commitment (nonce-based)
fn round1_generate_commitment(rng: &mut R) -> (Commitment, Scalar, Scalar) {
let chi1 = Scalar::random(rng);
let chi2 = Scalar::random(rng);
let d1 = G1Point::from_secret_key(&chi1); // hash_to_curve simplified
let d2 = G2Point::from_secret_key(&chi2);
((d1, d2), chi1, chi2)
}
// Coordinator: Aggregate commitments using Lagrange interpolation coefficients
fn aggregate_commitments(
commitments: &[(usize, Commitment)],
signing_set: &[usize],
) -> Commitment {
let mut d1 = G1Point::identity();
let mut d2 = G2Point::identity();
for &id in signing_set {
let comm = commitments.iter().find(|(i, _)| *i == id).unwrap().1;
let lambda_i = lagrange_coefficient(signing_set, id); // Compute Lagrange coeff
d1 += comm.0 * lambda_i;
d2 += comm.1 * lambda_i;
}
(d1, d2)
}
// Round 2: Each signer computes signature share for L2 block hash
fn round2_signing_share(
secret_share: Scalar,
chi1: Scalar,
l2_block_hash: &[u8],
aggregate_D: &Commitment,
) -> SigningShare {
let rho = hash_to_scalar(b"FROST", l2_block_hash, &aggregate_D.0.serialize(), &aggregate_D.1.serialize());
let z_i = secret_share * rho + chi1;
z_i
}
fn lagrange_coefficient(set: &[usize], id: usize) -> Scalar {
// Placeholder for Lagrange basis polynomial evaluation at id
Scalar::one() // Simplified
}
fn hash_to_scalar(domain: &[u8], data: &[u8], extra: &[u8]) -> Scalar {
// Secure hash-to-scalar (e.g., expand_message)
Scalar::from_bytes_mod_order(&sha256::digest(domain, data, extra)[..32]).unwrap()
}
``` This pseudocode omits critical components such as commitment verification, deserialization, partial signature aggregation into a Schnorr-like signature, and proof-of-possession checks. Coordinators must securely broadcast aggregate commitments without trusting malicious nodes. Consult the FROST RFC (draft-irtf-cfrg-frost) and audit with libraries like `frost-ed25519` or BLS variants before deployment.
Cautiously, tune round timeouts to balance liveness against denial-of-service; a sluggish node drags the quorum. In practice, optimistic responsiveness assumes honest majorities, falling back to Layer 1 proofs if thresholds fail. This mirrors escape hatches in centralized setups but hardens them cryptographically, as Quantstamp frameworks advocate.
Seamless Integration into L2 Operations
Embed TSS into the sequencer lifecycle: transactions flow into a decentralized mempool, perhaps gossip-sub propagated. Proposers compete via auctions or rotations, threshold-sign the batch, then submit to the rollup's data availability layer. For cross-rollup interop, as Ethereum Research models suggest, shared sequencers like Maven 11's amplify sovereignty; each rollup verifies the threshold sig independently.
Challenges arise in latency: arXiv benchmarks show threshold paths hitting 7δ proposal times, tolerable for most DeFi but tight for high-frequency trading. Mitigate with TEEs for off-chain computation, though Dagstuhl warns of placement pitfalls - host TEEs on honest nodes to dodge censorship vectors.
Morph's community-driven network exemplifies this: OP-ZK hybrid with decentralized sequencers yields scalability sans single points. Yet, I caution against over-optimism; real deployments, per developer anecdotes, grapple with node collusion in low-stakes pools.
Bolstering Key Management and Resilience
Secure shares demand HSMs or TEEs, audited for side-channels. Dynamic protocols enable node rotations: add a newcomer by threshold-signing their share inclusion, expelling laggards via slashing. LuxFi's library streamlines this across chains, supporting post-quantum LWE variants - essential as quantum threats near.
Test exhaustively: simulate Byzantine faults, where t-1 nodes collude. Chainlink's sequencer primer stresses batching efficiency; threshold overheads must not eclipse centralization gains. In my view, pair with economic incentives - stake-slashing for censorship attempts - to align nodes, echoing Metis's MPC proofs.
Real-World Deployment Insights and Pitfalls
Practical zero-trust TSS, as ePrint archives detail, scales to hundreds in crypto systems, but L2 pools start smaller for stability. Monitor for griefing attacks, where nodes sign invalid partials; robust verification aborts cleanly. Community polls reveal 70% of devs prioritize liveness over purity, favoring t=n/2 and 1.
Edge cases demand scrutiny: network partitions split quorums, risking dual-signed forks. Enforce via Layer 1 finality gadgets, preserving L2 censorship resistance. Opinionated take: shun naive ECDSA ports; FROST on BLS or Schnorr future-proofs better.
Armed with these layers, developers craft sequencers that defy coercion, transaction data flowing uncensorably. Threshold signatures, wielded judiciously, cement unbreakable L2 foundations amid surveillance swells.





No comments yet. Be the first to share your thoughts!